tl;dr: I built a free and open service, bugalert.org, that is powered by GitHub.
When the Log4j vulnerability was first discovered, it was reported, as most are, on Twitter. 13 hours passed between the time it was disclosed on Twitter to the time LunaSec put out their widely-shared blog post and a CVE identifier was allocated, and 5 hours passed after that before I saw it up at the top of Hacker News. By then, precious time for reacting had been completely lost; it was past midnight in most of the U.S.
Picking from two non-ideal choices
As a security professional, I feel as though I have only two choices:
- Closely follow the InfoSec community on Twitter, and all the drama that comes with it (🤢), or,
- Find out about things once they are in the top 3-5 posts of my Reddit or Hacker News feeds, hours and hours late (very often, after kids are in bed and dinner cleanup is done).
The industry simply must move faster. As reported by Cloudflare and others during the Log4j incident, attacks were already massively ramping up by the time after the issue was reported on Twitter. I don’t find it comforting when the bad guys have nearly a day of head start, simply because it takes a long time to make everyone aware there is a problem in the first place.
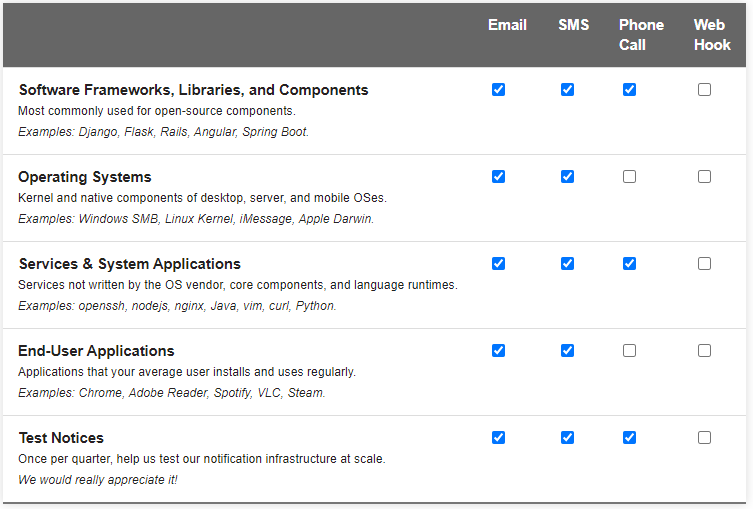
Adding a third option, Bug Alert
Over the past few weeks, I’ve developed bugalert.org, a free and open-source service for alerting security and IT professionals of high-impact and 0day vulnerabilities by email, SMS, and phone calls (and via Twitter). Subscribers choose the types of issues they care about (e.g. ‘Operating Systems’ or ‘Software Libraries’), and how they want contacted for each of those types. Bug Alert exists to make you aware of get-out-of-bed and cancel-your-date-night types of issues, so notices will be rare, clear, and concise.
Bug Alert is not the most beautiful site ever made, but it’s simple, functional, cares about your personal data, and most importantly, entirely open to the community. Vulnerability notices can be submitted by anyone in the world via Pull Request, and, once merged, will be posted on the website and delivered to subscribers via their preferred communication method in under 10 minutes.
I need some assistance from the security community to make this endeavor work. First, I need a team of volunteers from around the world who can review and rapidly merge GitHub pull requests detailing new issues, as they come in. Volunteers need to be kind, level-headed individuals who are willing to engage a diverse set of people in the security community with unwavering professionalism and no ego. If that sounds like you, open a GitHub issue letting me know! I appreciate your support.
Second and equally important, our community will need contributors who, upon news of a severe issue, stand ready and able to write notices clearly and concisely, and assign a severity level. If that sounds like you, all you need to do is open a Pull Request based on the notice template and the volunteer team will review and merge.
Discussion
If you have questions, concerns, or you feel like there’s something we could do differently, I would love to hear about it.

As someone in info security, I also have to echo how chaotic it can be trying to keep tabs on the latest “game-changing” bugs and breaches.
My tactic is also twitter and reddit, although I also monitor openCVE emails. But yeah, it’s a pretty chaotic and easy-to-miss environment so bravo on trying something new.
LikeLike
Would be nice if the site worked without Javascript (which has *regular* security issues!)…
LikeLike